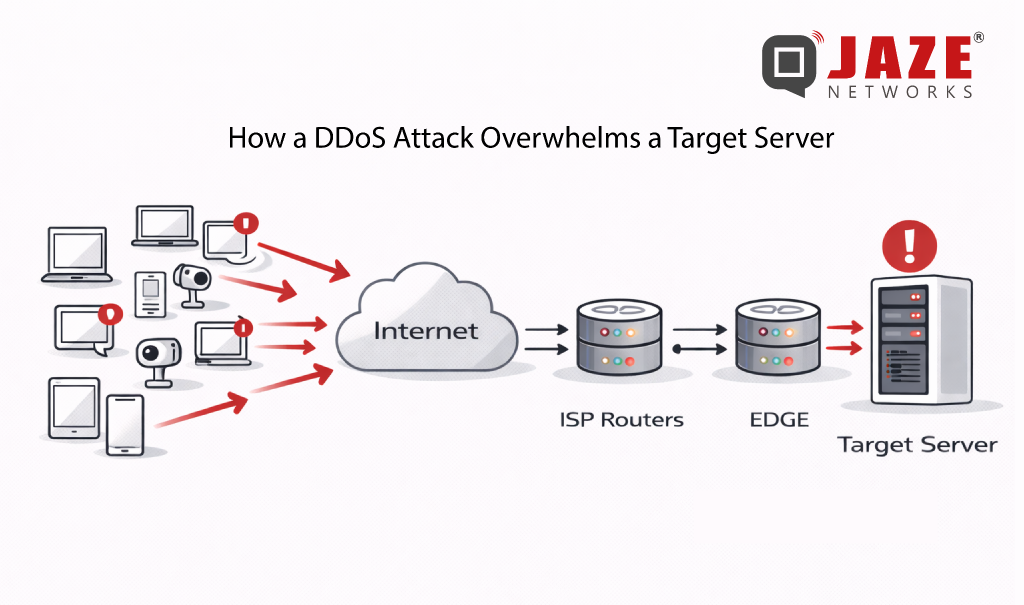
DDoS attacks are no longer rare, large-scale events. Volumetric floods exceeding hundreds of gigabits per second are now routine — and for ISPs, the damage isn’t just to the targeted subscriber. Congestion cascades across shared infrastructure, degrading service for everyone on the network. The question isn’t whether your network will face a DDoS attack. It’s how fast you can stop one.
BGP Flowspec is the answer most network operators are turning to — and for good reason. It combines the speed of BGP route propagation with the precision of granular traffic filtering, giving ISPs surgical control over attack traffic without disrupting legitimate users.
From Blunt to Precise: The Evolution Beyond RTBH
Before Flowspec, Remote Triggered Black Hole (RTBH) filtering was the go-to mitigation tool. RTBH works by routing all traffic destined for an attacked IP address to a null route — effectively dropping everything. It works fast, but it’s indiscriminate: legitimate traffic to that host gets silently discarded alongside the attack traffic.
BGP Flowspec (defined in RFC 5575 and extended in RFC 8955) was developed to solve this problem. Rather than blackholing an entire destination, Flowspec lets operators define detailed traffic rules based on multiple attributes simultaneously — and distribute those rules across the network in seconds via BGP.
What Makes BGP Flowspec Powerful
Flowspec rules can match traffic using a combination of:
• Source and destination IP addresses or prefixes
• Source and destination port numbers
• IP protocol (TCP, UDP, ICMP, etc.)
• Packet length and DSCP markings
• TCP flags (SYN, ACK, RST, etc.)
Once a rule is created, Flowspec propagates it to all BGP-peered routers — including upstream providers and transit peers — in real time. Instead of one appliance scrubbing traffic at a single point, the entire network perimeter reacts simultaneously.
Supported actions include rate-limiting specific traffic types, redirecting flows to scrubbing centers, tagging packets with DSCP values for QoS treatment, or dropping traffic outright. This flexibility makes Flowspec equally useful for volumetric UDP floods, TCP SYN attacks, and reflection/amplification attacks.
How Mitigation Works in Practice
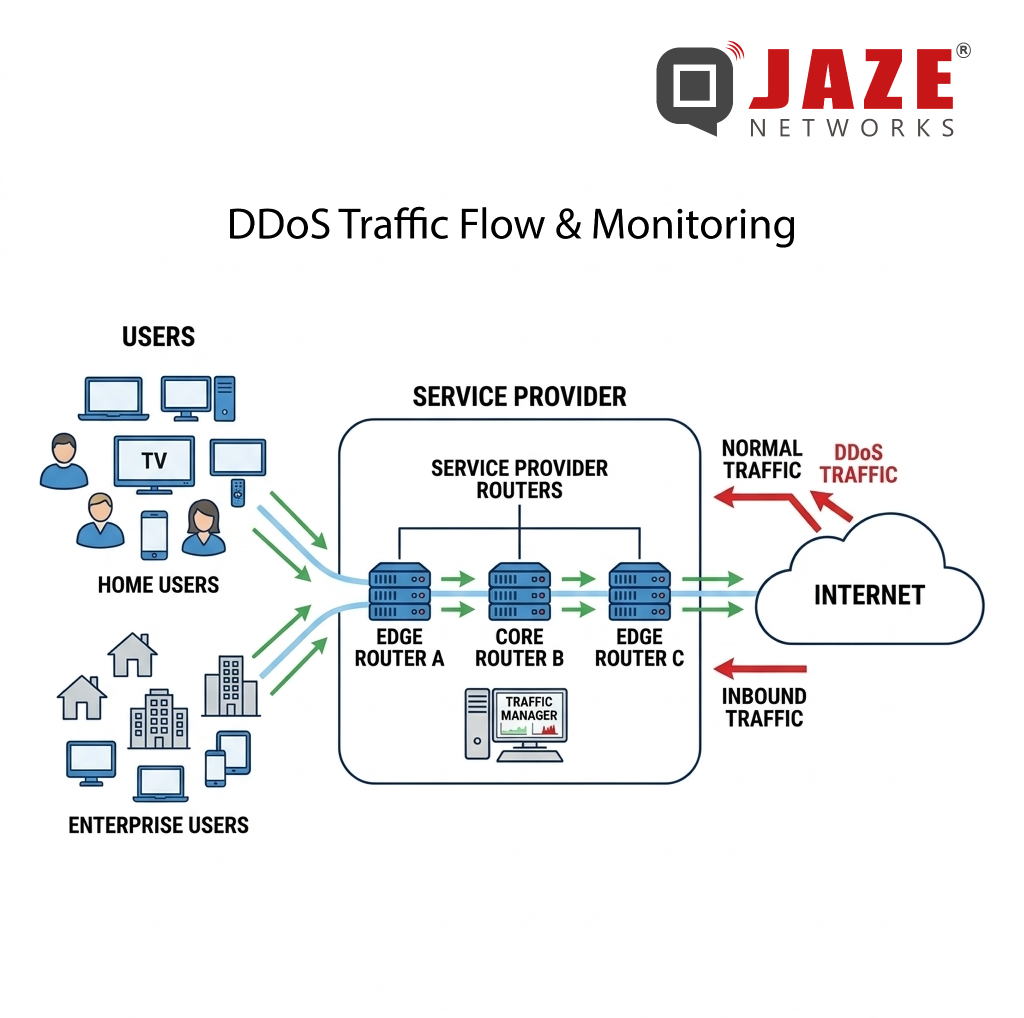
In a typical deployment, traffic telemetry — from NetFlow, IPFIX, or sFlow — is continuously analyzed by a detection system. When an attack signature is identified, the system automatically generates a Flowspec rule and announces it via BGP to all participating routers.
The entire cycle — detection, rule creation, propagation, enforcement — can complete in under 30 seconds. At attack scale, that speed is the difference between a 5-minute blip and a 45-minute outage.
Because Flowspec rules target specific traffic characteristics rather than IP addresses, legitimate users on the same subnet or hosting the same services are unaffected. The attack is blocked; normal traffic continues.
Vendor Support and Deployment Considerations
BGP Flowspec is supported across all major network equipment vendors — Cisco, Juniper, Huawei, Nokia, and Arista all implement it natively in their router operating systems. However, implementation depth varies: some platforms support only basic match criteria, while others support the full RFC 8955 attribute set.
For ISPs deploying Flowspec, key planning decisions include:
• Which routers will act as Flowspec clients (receiving and enforcing rules)
• Whether upstream transit providers also support Flowspec peering
• How detection thresholds are tuned to minimize false positives
• Whether mitigation is manual, semi-automated, or fully automated
Automated Flowspec deployment — where detection and rule announcement happen without human intervention — is now the standard approach for ISPs handling large subscriber bases. Manual processes are too slow when an attacker can saturate uplinks in seconds.
Flowspec and RTBH: Complementary, Not Competing
Flowspec doesn’t make RTBH obsolete. For attacks where the traffic source is clearly identified and the targeted IP has no legitimate inbound traffic (a server in maintenance, for example), RTBH remains faster to deploy and simpler to manage.
A mature ISP DDoS strategy uses both: RTBH for immediate, coarse-grained isolation and Flowspec for precise, sustained mitigation that preserves service availability for other subscribers on the same prefixes.
Jaze ISP Manager provides scalable IPFIX logging which can be integrated with DDoS protection systems for real-time DDoS detection and mitigation. In integration with BGP routers supporting RTBH and BGP Flowspec , ISPs can detect, respond to, and neutralise DDoS attacks before service is disrupted — keeping subscribers connected and SLAs intact.
Click here to see how Jaze ISP Manager helps in delivering scalable IPFIX logging services.