Internet Service Providers (ISPs) and enterprises face mounting pressure to secure their networks while ensuring seamless user experiences in the fast-paced digital era. The Authentication, Authorization, and Accounting (AAA) framework provides a structured approach to manage network access, prevent misuse, and maintain compliance.
What is AAA in Networking?
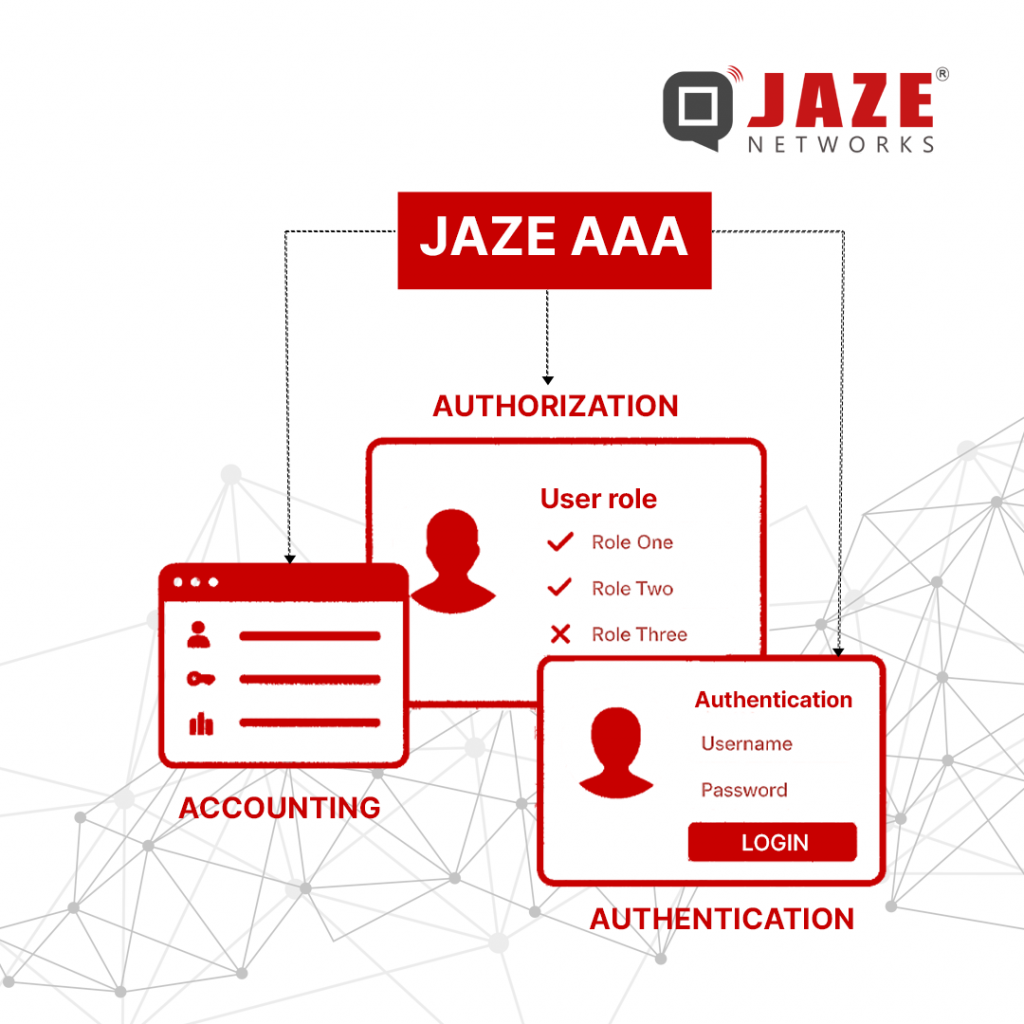
AAA stands for:
- Authentication – Confirming the identity of a user or device before granting access.
- Authorization – Defining what authenticated users are allowed to do within the network.
- Accounting – Recording user activity for billing, auditing, and security analysis.
Together, these three processes create a reliable system that ensures only the right people get the right level of access—while all activities are logged for accountability.
Why AAA Matters for ISPs and Businesses
1. Stronger Security at Scale
Unauthorized access can lead to service abuse, downtime, and regulatory risks. AAA protocols ensure only verified users connect to the network, reducing threats from both external attackers and internal misuse.
2. Smarter Access Control
With authorization policies, ISPs can assign access levels based on roles—customers, staff, or partners—ensuring sensitive systems remain protected.
3. Transparent Usage and Billing
Accounting helps providers monitor how network resources are used. For ISPs, this is especially valuable for bandwidth management, billing accuracy, and detecting unusual traffic spikes.
4. Compliance and Trust
Governments and regulators demand traceability of network activity. Accounting logs serve as digital evidence to meet compliance requirements and reassure customers about data security.
Common AAA Protocols
Different protocols implement AAA in unique ways. Here are the most widely adopted:
- RADIUS (Remote Authentication Dial-In User Service)
The most common AAA protocol, RADIUS works well for managing customer access in broadband and wireless networks. It uses UDP, making it fast and lightweight, but less granular than TACACS+. - TACACS+ (Terminal Access Controller Access-Control System Plus)
Preferred for device administration, TACACS+ provides detailed control over user privileges. Operating over TCP, it offers more reliable communication and fine-grained policy enforcement. - Diameter
An advanced successor to RADIUS, Diameter supports modern applications and offers stronger security and scalability. It is increasingly adopted in mobile and LTE/5G environments.
Implementing AAA in ISP Environments
For ISPs and large businesses, a well-structured AAA setup is critical. The implementation usually involves:
- Choosing the right protocol – RADIUS for customer access, TACACS+ for device control, or Diameter for modern mobile networks.
- Setting up AAA servers – Servers validate credentials, assign permissions, and log activities.
- Integrating with network devices – Routers, switches, and access points communicate with AAA servers to enforce security policies.
- Defining user policies – Assign roles and permissions based on organizational needs, ensuring least-privilege access.
- Monitoring and auditing – Regularly reviewing logs to detect anomalies and maintain compliance.
Best Practices for ISPs Using AAA
To get the most out of AAA frameworks, operators should:
- Adopt Multi-Factor Authentication (MFA) – Adding a second layer of verification drastically improves security.
- Encrypt communication – Protect sensitive exchanges between devices and AAA servers.
- Update access rules regularly – Policies should evolve with business needs and emerging threats.
- Automate monitoring – Real-time log analysis can quickly flag suspicious behavior before it becomes a major issue.
- Plan for redundancy – Deploy multiple AAA servers to avoid outages and ensure continuous service availability.
AAA in the Future of ISP Operations
As ISPs expand services into fiber, 5G, and enterprise networking, the demand for scalable, automated AAA systems will only grow. Cloud-native AAA platforms are already emerging, offering flexibility and real-time policy enforcement across distributed infrastructures.
For ISPs and enterprises alike, AAA is no longer optional—it’s the foundation of secure, reliable, and accountable network access. By choosing the right protocols, enforcing strong access policies, and embracing best practices, operators can strengthen security, streamline operations, and build customer trust.
Jaze ISP Manager delivers carrier-grade AAA with centralized authentication, authorization, and accounting to secure broadband, enterprise, and public access networks. It integrates seamlessly with RADIUS and TACACS+ for subscriber management and device administration across distributed infrastructures.
ISPs can enforce role-based access policies, streamline user onboarding, and ensure compliance with regulatory requirements. Built-in redundancy guarantees high availability, while real-time accounting provides transparency for usage, billing, and auditing. By combining automation with AAA architecture, Jaze enables operators to deliver uninterrupted connectivity, faster troubleshooting, and reliable service at scale.
Click here to know more